|
The Great Pyramids of Egypt have long fascinated and mystified humanity with their colossal size and precise engineering. While many theories abound about their purpose and construction, one intriguing perspective suggests that these ancient monuments were more than just tombs for pharaohs—they were sophisticated generators of clean energy. In his book "Unveiling the Pyramid Power," author Christopher Dunn delves into this theory, presenting compelling evidence and cutting-edge research that sheds new light on the true function of the pyramids. Dunn begins by exploring the intricate design of the Great Pyramid at Giza, from its internal chambers to its massive stone blocks to the enigmatic pyramidion on top. He proposes that the pyramid was engineered to harness seismic energy, effectively acting as an energy-harvesting machine for the ancient Egyptian civilization. Drawing parallels with the work of renowned inventor Nikola Tesla, Dunn suggests that the pyramid builders tapped into a universal knowledge of energy manipulation. One key aspect of Dunn's theory is the concept of harmonizing seismic energy to stimulate the release and collection of electrons in the Earth's crust. By precisely aligning the pyramid's structure and utilizing specific materials, the builders were able to harness this natural energy source and convert it into usable electricity. Dunn points to recent research on phenomena like "earthquake lights" and acoustic frequency measurements to support his claims, demonstrating how the ancient Egyptians may have been inspired by these natural occurrences. The book delves into the details of the pyramid's construction and design, highlighting features such as the shafts of the Queen's Chamber and the scorch marks on the ceiling of the Grand Gallery. Dunn argues that these elements provide further evidence of the pyramid's energy-harvesting capabilities, with the large void discovered above the Grand Gallery in 2017 adding to the mystery and significance of the structure. Throughout "Unveiling the Pyramid Power," Dunn presents technical appendices written by experts and top researchers, further bolstering his arguments with scientific analysis and data. He also explores the implications of this ancient technology for modern civilization, suggesting that remnants of pyramid power may still exist, waiting to be rediscovered and harnessed for nonpolluting energy solutions. In conclusion, "Unveiling the Pyramid Power" offers a fascinating reinterpretation of one of the world's most iconic architectural wonders. By challenging conventional views and presenting compelling evidence, Christopher Dunn invites readers to reconsider the true purpose and potential of the Great Pyramids of Egypt. referencesDunn, Christopher. Giza: The Tesla Connection: Acoustical Science and the Harvesting of Clean Energy. Bear & Company, 30 Jan. 2024.
0 Comments
In a recent interview, Mike Benz, Executive Director of the Foundation for Freedom Online and former Deputy Assistant Secretary at the U.S. Department of State, discussed the evolving landscape of free speech on the Internet and its intersection with geopolitics. According to Benz, free speech on the Internet has been a strategic tool in the realm of statecraft since the early days of its privatization.
Benz highlighted Google's origin as a DARPA grant and its transformation into a military contractor, emphasizing the military-industrial roots of prominent tech companies. He pointed to a paradigm shift in warfare following the annexation of Crimea, leading NATO to acknowledge the importance of controlling the media and social media ecosystem for electoral influence—a concept known as the Gerasimov doctrine. Notably, NATO identified the manipulation of media and social media as a significant threat, with the primary concern being the potential impact on domestic elections across Europe. The interview included a quote from a four-star general, questioning the fate of the U.S. military when major news outlets are reduced to the scale of social media pages. Benz expressed concern about the rise of the censorship industry, describing it as a fundamental inversion of democracy. He argued that the current state of affairs resembles a form of military rule, where controlling narratives and information flow takes precedence. In his view, the essence of democracy has been distorted, with power shifting towards aligning non-governmental organizations, financial entities like BlackRock, major media outlets, and community activist groups. The interview sheds light on the intricate relationship between free speech, technology, and geopolitical dynamics, raising important questions about the impact of information control on democracy and the evolving nature of warfare in the digital age. The national security state is the main driver of censorship and election interference in the United States. "What I’m describing is military rule," says Mike Benz. "It’s the inversion of democracy." transcript
2030 UnMasked is a documentary revealing the connection between Covid-19, Vaccines, Masks, the Banking System, and the upcoming “Great Reset”.
This documentary is for anyone realizing something is wrong in the world. Especially for those “just waking up”. It’s uncomfortable to learn that so many things you’ve been told are untrue and this documentary is intended to help make sense of WHY so many things are happening, HOW they are happening, and also WHAT you can do about it. We can’t obey our way out of tyranny. Mass disobedience is the best way to move forward and helping as many people become AWARE is one of the first places to start.
Welcome, Esteemed Globalist Supergopher. Here is your access link to the secret online briefing session of the Committee of United Nazis, Tyrants and Sociopaths. On today’s livestream, your deep state briefer will walk you through what we’re telling the public about our ambition to transform the human species through biodigital technologies . . . and reveal what we’re actually doing to engineer a perfectly compliant, perfectly controlled, cattle-like subspecies.
Vandana Shiva is an Indian scholar, environmental activist, physicist, food sovereignty advocate, and anti-globalization author. Based in Delhi, Shiva has written more than 20 books. Shiva founded the Research Foundation for Science, Technology, and Natural Resource Policy (RFSTN), an organization devoted to developing sustainable methods of agriculture, in 1982. She has traveled the world spreading a powerful message of oneness and interconnectedness.
Widespread poverty, social unrest, and economic polarization have become our lived reality as the top 1% of the world’s seven-billion-plus population pushes the planet―and all its people―to the social and ecological brink. Vandana Shiva takes on the billionaire dictators of Gates, Buffet, and Mark Zuckerberg, as well as other modern empires like Big Tech, Big Pharma, and Big Ag, whose blindness to the rights of people, and to the destructive impact of their construct of linear progress, have wrought havoc across the world. Their single-minded pursuit of profit has undemocratically enforced uniformity and monocultures, division and separation, monopolies and external control―over finance, food, energy, information, healthcare, and even relationships. Basing her analysis on explosive facts, Shiva exposes the 1%’s model of philanthrocapitalism, which is about deploying unaccountable money to bypass democratic structures, derail diversity, and impose totalitarian ideas based on One Science, One Agriculture, and One History. Instead, Shiva calls for the resurgence of:
With these core goals, people can reclaim their right to: Live Free. Think Free. Breathe Free. Eat Free.
Communist Subversion Part 1 provides a high level overview on the many layers to understanding the culprits involved in the New World Order. Part 1 provides a review and commentary by Jeremy Elliott on the classic works of G. Edward Griffin and Yuri Bezmenov as they relate to the New World Order and current events.
G. Edward Griffin provides details on the mysterious and infamous "They," the Secret Societies, the puppet-masters behind the scenes who control the governments of the world through carefully constructed "Rings of Power." These power groups maintain generational plans for the implementation of a world wide communistic government, ushering in a New World Order. Griffin notes that this single unified government aspiration is enacted using:
...which leads to the consolidation of all national sovereignty, into the hands of a small, but elite group, in the "Rings of Power."
Guided by the meticulous work of Dr. David E. Martin, Plandemic II: Indoctornation, tracks a three decade-long money trail that leads directly to the key players behind the COVID 19 pandemic. David Martin is the creator of the world’s first quantitative public equity index – the CNBC IQ100. He served as Chair of Economic Innovation for the UN-affiliated Intergovernmental Renewable Energy Organization and has served as an advisor to numerous Central Banks, global economic forums, the World Bank and International Finance Corporation, and national governments. Dr. Martin has pioneered global programs to bring corporate and stock market transparency to multi-national extractive industries and has been instrumental in bringing the world’s largest white-collar criminals to justice.
References
Who is Bill Gates? A software developer? A businessman? A philanthropist? A global health expert?
This question, once merely academic, is becoming a very real question for those who are beginning to realize that Gates' unimaginable wealth has been used to gain control over every corner of the fields of public health, medical research and vaccine development. And now that we are presented with the very problem that Gates has been talking about for years, we will soon find that this software developer with no medical training is going to leverage that wealth into control over the fates of billions of people. The pandemic presents an opportune time to get re-acquainted with Zach Bush.
A triple board-certified physician specializing in internal medicine, endocrinology and hospice care, today’s guest is an internationally recognized educator, speaker and authority on all facets of well-being. Focused on the relationship between the microbiome, disease and food production systems, Zach is the founder of Seraphic Group, an organization devoted to developing root-cause solutions for human and ecological health in the sectors of big farming, big pharma, and Western Medicine at large He is also the founder of Farmers Footprint, a non-profit coalition of farmers, educators, doctors, scientists, and business leaders aiming to expose the deleterious human and environmental impacts of chemical farming and pesticide reliance — while simultaneously offering a path forward through regenerative agricultural practices to rebuild living biodiversity and ultimately reverse climate change. To me, Zach is a master healer. A man I call a friend. And a critical voice in the conversation we need to have in this unprecedented moment of global calamity. Without minimizing the profound severity of our current situation, I cannot overstate the unique opportunity we are being gifted. Like an addict’s moment of clarity, the pandemic presents a singular occasion to break the chains of denial that imprison us. A moment to objectively examine that which no longer serves us. The behaviors that repeatedly lead us astray. An economic system that demands constant growth at the cost of the collective good. A political system that preys on fear to divide. A conglomerated food apparatus that foments disease. A pharmaceutical complex that relies upon that disease to create dependency. And ultimately a collective obsession with ego, power, money, and material consumption that is rapidly eroding our biosphere, degrading our integrity — and separating us from others, ourselves and our innate divinity. I aspire that we emerge from this planetary wake up call not as victims, but empowered — armed with greater clarity to reimagine and actualize a better, more sustainable, purposeful, intentional and fulfilling life experience for ourselves, our loved ones, future generations and frankly the world at large. I can think of few people better equipped to traverse this terrain than Zach, alongside me for his fourth appearance on the show. Well worth your undivided attention, today he shares his unique perspective on the coronavirus epidemic in a conversation that goes behind what is happening. How to best navigate it. And what the pandemic signifies for humanity and the future of planetary ecology. The universe is the internet is the library is the internet is the universe. Or is it? And if so, who are the librarians? And if we have all the information we can ever want, does that mean we have knowledge or wisdom? If not, how do we make it? Or who will make it for us? Join James in this classic "Film, Literature and the New World Order" examination of “The Library of Babel” by Jorge Luis Borges.
What is the "science of the government?"
On April 13th 1953, newly appointed CIA director Allen Dulles signed off on MKUltra, the CIA’s top secret mind control project. Three days before that Dulles gave a speech on the battle for mens minds to justify it. For Dulles it was a missive into a newly declared battle for the minds of men and would come just weeks after he became CIA director as a countermeasure to Soviet “brainwashing”. Dulles speech effectively launched MKUltra, he gave a plausible reason for the dark and disturbing research, he would later sign a memo that created the CIAs most notorious secret research project just three days later and ironically only a few weeks after the death of Stalin. “The Minds of Men” is a 3+ year investigation into the experimentation, art, and practice of social engineering and mind control during the Cold War — a mind-bending journey into the past that gives startling insight into the world we are living in today. It reveals [redacted]. Our economy is based on consumption and advertising is the arm of creating artificial demand. And without that arm, we wouldn’t have people aspiring to things that are highly irrational. When advertising presents something that seems to be what some people want, it spreads like a virus and then everybody wants it, because it is an issue of social inclusion, which is a part of our biology, because that is how we identify. We identify and define ourselves by how others see us and how we are included in the group.
So it manipulates our most primal sense of humanity in order to sell things. If we didn’t have that arm in our consumption-based society since the Industrial Revolution, the economy would collapse. That is a very unique point to make because when you first start an economy like in the agrarian society, you’re meeting demand right? That’s the point and that makes sense. But at some point this had to change because when you have such a highly-efficient, productive economy that we have today, at least in the technical sense of what we can create, you have to have demand created now. That is one of the central flaws of market economics or capitalism that has come to fruition today, not only destroying human psychology, but destroying the environment simultaneously, because you have an insatiable culture that has been literally generated. And then progress is defined by what we produce. The more you buy, the more you own. That must be progress now. It’s a kind of cultural violence. The more people promote materialistic values, the more they want more and more this and that, the more they flaunt this type of phenomenon, the more they create cultural violence. Because if you create a society that thrives in this type of self-identification, you are basically also promoting not only the destruction of the environment, but the diminishment of others, because you are saying, “I can afford this. I have the status and I am better for than and this person can’t.” And we see that phenomenally amplified today in the modern world. I often wonder what a world would be like without advertising, which would be a world without marketing and markets, and I can tell you it would be a far more peaceful and sustainable and amiable and humane than what we see today. Chamath Palihapitiya, Founder, CEO Social Capital and former Facebook executive, warned about the unintended consequences of social media at Stanford Graduate School of Business: "I think we have created tools that are ripping apart the social fabric of how society works. The short-term, dopamine-driven feedback loops we’ve created are destroying how society works. No civil discourse, no cooperation; misinformation, mistruth. You are being programmed"
As the former executive states, we compound the problems in, and curate, our lives around this perceived sense of perfection because we get rewarded in these short-term signals (hearts, likes, thumbs up), and we conflate that with value and truth. Instead, what it really is, is fake, brittle popularity, that is short-term, and it leaves you even more (admit it) vacant and empty. Watch the original, full-length video here During his View From The Top talk, Chamath Palihapitiya, founder and CEO of Social Capital, discussed how money is an instrument of change which should be used to make the world a better place. “Money drives the world for better or for worse. Money is going to be made and allocated – you have a moral imperative to get it and then use it to make a difference.“
Now openly admitted, governments and militaries around the world employ armies of keyboard warriors to spread propaganda and disrupt their online opposition. Their goal? To shape public discourse around global events in a way favorable to their standing military and geopolitical objectives. Their method? The Weaponization of Social Media.
U.S. President Donald Trump on Friday, January 19, 2018 said he signed into law a bill renewing the National Security Agency’s warrantless internet surveillance program. “Just signed 702 Bill to reauthorize foreign intelligence collection,” Trump wrote on Twitter, referring to legislation passed by the U.S. Congress that extends Section 702 of the Foreign Intelligence Surveillance Act (FISA). The law is renewed for six years and with minimal changes the National Security Agency (NSA) program, which gathers information from foreigners overseas and also collects an unknown amount of communications belonging to Americans. Without Trump’s signature, Section 702 had been set to expire on Friday, though intelligence officials had said the surveillance program could continue to operate until April. Under the law, the NSA is allowed to eavesdrop on vast amounts of digital communications from foreigners living outside the United States via U.S. companies like Facebook, Verizon, and Google. But the program also incidentally scoops up Americans’ communications, including when they communicate with a foreign target living overseas, and can search those messages without a warrant. The White House, U.S. intelligence agencies and congressional Republican leaders have said the program is indispensable to national security, vital to protecting U.S. allies and needs little or no revision. Privacy advocates say it allows the NSA and other intelligence agencies to grab data belonging to Americans in a way that represents an affront to the U.S. Constitution. ReferencesVolz, D. (2018). Trump signs bill renewing NSA's internet surveillance program. [online] Reuters. Available at: https://www.reuters.com/article/us-usa-trump-cyber-surveillance/trump-signs-bill-renewing-nsas-internet-surveillance-program-idUSKBN1F82MK?feedType=RSS&feedName=domesticNews [Accessed 23, Jan. 2018].
A design flaw, more accurately described as an exploit, affecting owners of Windows PCs with Intel processors has been discovered. A software update has been released by Microsoft that fixes the security flaw but could cause the performance of the Intel chips to slow down by as much as 30%. The Intel processor flaw is related to software "kernels" - the core of an operating system. At the most basic level, the kernel handles the interactions between the operating system and the processor. In this case, the issue apparently is linked to an exploitable security flaw in the way that the kernel of the Microsoft Windows operating system interacts with Intel processors. In theory, a hacker could exploit this undesirable interaction, using malware, and bypass normal security measures, enabling hackers to "observe" passwords, encryption keys, and other sensitive personal data on computers. The underlying root of the issue has to do with Intel's own processors. Intel-based PCs running the Linux operating system suffer from the same problem. This could have big implications for cloud computing, given that Linux is popular in datacenters. Additionally, Apple Mac computers are also reportedly affected and will require an update to fix, as the flaw is primarily based in the physical Intel chip design. It is currently unclear how the flaw and any update fixes will affect Apple computers. Initial reports indicated that the security flaw was limited to Intel processors, but chipmaker ARM has since said that chips based on its technology are also affected. Intel, AMD, ARM, original equipment manufacturers, and operating system vendors, have been collaborating to come up with fixes and mitigations for the issue since the discovery of the exploit. Repairs will involve software and firmware updates on both the hardware and the software sides. Intel CEO States Flaw Discovered Months Ago According to Intel CEO Brian Krzanich, the widespread microprocessor flaw was discovered by Google months ago, in June of 2017. Even more alarming is the discovery of $24 million worth shares sold by Mr. Krzanich, months after he had been informed of the security vulnerability — but before the problem was publicly known. The stock sale left Krzanich with just 250,000 shares of Intel stock — the minimum the company requires him to hold under his employment agreement. The sell-off could draw even more scrutiny now, given the news about the security vulnerability and the timing of when Intel knew about it. Intel claims Krzanich's sale was preplanned and had nothing to do with the newly disclosed chip vulnerability— but that plan was put in place months after it learned of the chip vulnerability. References Villas-Boas, A. (2018). Intel CEO: Google discovered the chip problem 'months ago'. [online] Business Insider. Available at: http://www.businessinsider.com/intel-ceo-google-discovered-the-chip-flaw-months-ago-2018-1 [Accessed 9 Jan. 2018].
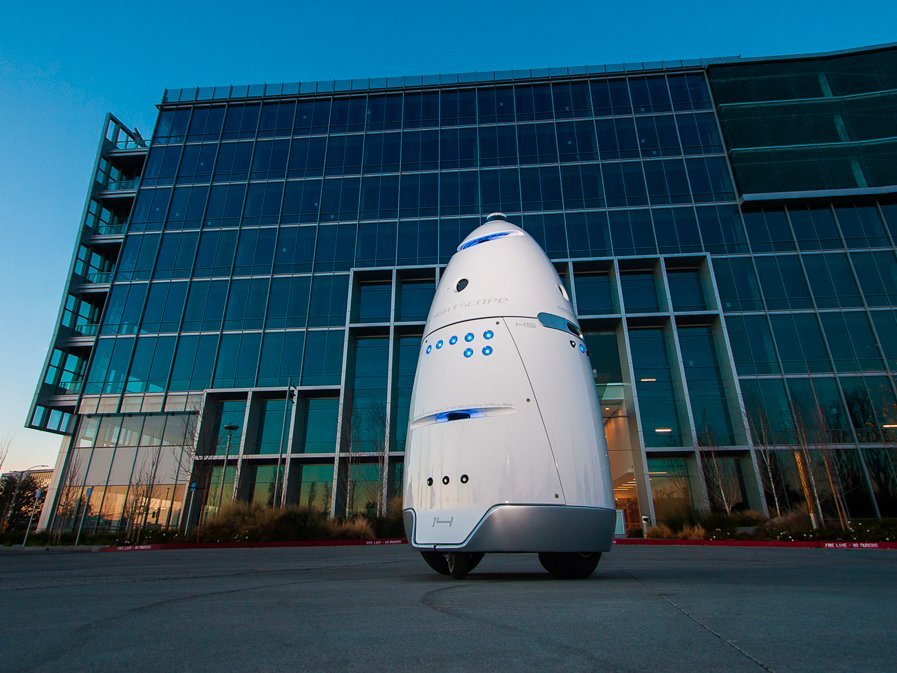
Villas-Boas, A. (2018). Windows PCs could get a big performance slowdown because of a flaw in Intel chips. [online] Business Insider. Available at: http://www.businessinsider.com/intel-cpu-flaw-big-performance-slowdow-windows-pc-2018-1 [Accessed 9 Jan. 2018]. Wolverton, T. (2018). Intel was aware of the chip vulnerability when its CEO sold off $24 million in company stock. [online] Business Insider. Available at: http://www.businessinsider.com/intel-ceo-krzanich-sold-shares-after-company-was-informed-of-chip-flaw-2018-1 [Accessed 9 Jan. 2018]. The San Francisco SPCA (a Society for the Prevention of Cruelty to Animals), an animal advocacy and pet adoption group, has deployed an autonomous robot in an effort to patrol local areas for crime and deter homeless people from setting up camps along the sidewalks. The City of San Francisco ordered the SPCA to keep its robot off the sidewalks or face a penalty of up to $1,000 per day for operating in the public right-of-way without a permit.
SPCA rents the robots for $7 an hour — $3 less than a security guard's hourly wage. Knightscope has over 19 clients in five US states. Most customers, including Microsoft, Uber, and Juniper Networks, put the robots to work patrolling parking lots and office buildings. The K9 robot circling the SPCA has drawn mixed responses. Within the first week of the robot's deployment, some people who were setting up a homeless encampment nearby allegedly put a tarp over it, knocked it over, and put barbecue sauce on all the sensors. One wonders what the human backlash will be once a vast portion of America's middle class realizes that it has been made obsolete courtesy of robots who can do its job faster, smarter, much more efficiently and for a fraction of the cost. References Green, A. (2017). Security robot that deterred homeless encampments in the Mission gets rebuke from the city. [online] Bizjournals.com. Available at: https://www.bizjournals.com/sanfrancisco/news/2017/12/08/security-robot-homeless-spca-mission-san-francisco.html [Accessed 19 Dec. 2017].
Robinson, M. (2017). Robots are being used to deter homeless people from setting up camp in San Francisco. [online] Business Insider. Available at: http://www.businessinsider.com/security-robots-are-monitoring-the-homeless-in-san-francisco-2017-12 [Accessed 19 Dec. 2017]. The Transportation Security Administration (TSA) plans to move forward with progressively implementing facial recognition and other biometric data into screenings at various airports across the United States. The agency began testing out the methods, which also include iris scans and fingerprints, on volunteers in their PreCheck program at airports over the summer. On November 1, the TSA announced plans to expand the program. The TSA Pre-Application program claims to enhance “aviation security by permitting TSA to better focus its limited security resources on passengers who are more likely to pose a threat to civil aviation, while also facilitating and improving the commercial aviation travel experience for the public.” Under the program, individuals are to submit biographic information (including, but not limited to, name, date of birth, gender, prior and current addresses, contact information, country of birth, images of identity documents, proof of citizenship/immigration status) and biometric data (such as fingerprints, iris scans, or facial images) to a TSA contractor, which forwards the information to the agency. From Pilot Program to National Policy In June and July of 2017, the TSA “launched a proof of concept initiative at Hartsfield-Jackson Atlanta International Airport and Denver International Airport to determine whether fingerprints from TSA Pre✓® Application Program applicants,” who volunteered to participate, could be used for identity verification. The TSA is currently “seeking a revision to the currently approved request to allow for the collection of additional biometrics, particularly facial images but may include other biometrics such as iris, from TSA Pre✓® Application Program applicants.” The TSA claims that "the regular collection of biometrics, such as facial images, will provide TSA with the ability to use those biometrics for identity verification at TSA checkpoints, potentially eliminating the need to show identity documents and improving both security and the customer experience.” Some privacy advocates disagree with the attempted expansion. According to the Electronic Frontier Foundation, the TSA’s push to expand its use of biometrics is part of a broader push by the Department of Homeland Security (DHS) to nationalize the collection and use of biometric data. According to an assessment by the DHS, in 2016 the U.S. Customs and Border Protection (CBP) will operate a test at Hartsfield-Jackson Atlanta International Airport, in Atlanta, Georgia in order to identify reliable and cost-effective border management capabilities (such as verifying biometrics of departing travelers) that can be deployed nationwide and across multiple modes of travel. Photos of travelers taken during boarding will be compared against photos taken previously (U.S. passport, U.S. visa, and other DHS encounters) and stored in existing CBP systems. Prior to the departure of each flight, CBP will collect facial images and boarding pass information of all travelers, including U.S. citizens, as they pass through the passenger loading bridge to board their flight. CBP will use this data to test the ability of CBP data systems to confirm a traveler’s identity using a facial biometric comparison as the traveler departs from the United States. Initially, the DHS states that the data will be stored for no longer than one year after the test. Since then the DHS updated it's stance, stating "CBP retains biographic exit records for 15 years for U.S. citizens and lawful permanent residents and 75 years for non-immigrant aliens." These actions would be carried out without congressional authorization. Initially these practices were to be limited to international flights. However, according to John Wagner, deputy assistant commissioner at CBP, the TSA is now seeking to expand the collection of biometric data to domestic flights, as well. DHS Data in the Hands of Third Parties Concerns should also be raised regarding the storage of biometric data in the hands of third parties, including but not limited to airlines. DHS sub-agencies are sharing data with the FBI, and the TSA Pre-check program shares it with private companies it uses as contractors. Americans should be concerned about these proposals because the data collected—your fingerprint, the image of your face, and the scan of your iris—will be stored in the databases of the FBI, DHS, and other non-government third parties (such as commerical airlines and air authorities), which will be searched for immigration, law enforcement, and intelligence checks, including checks against latent prints associated with unsolved crimes. This vast data collection will create a huge security risk. As seen with the 2017 Equifax breach, no government agency or private company is capable of fully protecting your private and sensitive information. While losing your social security or credit card information may result in fraud, those numbers can easily be changed. On the other hand, if your biometrics get into the wrong hands, you can’t change your face. ReferencesDhs.gov. (2016). Departure Information Systems Test. [online] Available at: https://www.dhs.gov/sites/default/files/publications/privacy-pia-cbp-dis%20test-june2016.pdf [Accessed 15 Dec. 2017].
Dhs.gov. (2017). Traveler Verification Service (TVS). [online] Available at: https://www.dhs.gov/sites/default/files/publications/privacy-pia-cbp030-tvs-september2017.pdf [Accessed 15 Dec. 2017]. Lynch, J. (2017). TSA Plans to Use Face Recognition to Track Americans Through Airports. [online] Electronic Frontier Foundation. Available at: https://www.eff.org/deeplinks/2017/11/tsa-plans-use-face-recognition-track-americans-through-airports [Accessed 15 Dec. 2017]. Regulations.gov. (2017). Agency Information Collection Activities; Proposals, Submissions, and Approvals: TSA Pre-Check Application Program. [online] Available at: https://www.regulations.gov/document?D=TSA-2014-0001-0021 [Accessed 15 Dec. 2017]. Wedler, C. (2017). TSA Plans to Use Facial Recognition to Track Americans in US Airports. [online] The Anti-Media. Available at: http://theantimedia.org/tsa-facial-recognition-biometrics/ [Accessed 15 Dec. 2017]. |
This feed contains research, news, information, observations, and ideas at the level of the world.
Archives
May 2024
Categories
All
|


 RSS Feed
RSS Feed

