|
In a recent interview, Mike Benz, Executive Director of the Foundation for Freedom Online and former Deputy Assistant Secretary at the U.S. Department of State, discussed the evolving landscape of free speech on the Internet and its intersection with geopolitics. According to Benz, free speech on the Internet has been a strategic tool in the realm of statecraft since the early days of its privatization.
Benz highlighted Google's origin as a DARPA grant and its transformation into a military contractor, emphasizing the military-industrial roots of prominent tech companies. He pointed to a paradigm shift in warfare following the annexation of Crimea, leading NATO to acknowledge the importance of controlling the media and social media ecosystem for electoral influence—a concept known as the Gerasimov doctrine. Notably, NATO identified the manipulation of media and social media as a significant threat, with the primary concern being the potential impact on domestic elections across Europe. The interview included a quote from a four-star general, questioning the fate of the U.S. military when major news outlets are reduced to the scale of social media pages. Benz expressed concern about the rise of the censorship industry, describing it as a fundamental inversion of democracy. He argued that the current state of affairs resembles a form of military rule, where controlling narratives and information flow takes precedence. In his view, the essence of democracy has been distorted, with power shifting towards aligning non-governmental organizations, financial entities like BlackRock, major media outlets, and community activist groups. The interview sheds light on the intricate relationship between free speech, technology, and geopolitical dynamics, raising important questions about the impact of information control on democracy and the evolving nature of warfare in the digital age. The national security state is the main driver of censorship and election interference in the United States. "What I’m describing is military rule," says Mike Benz. "It’s the inversion of democracy." transcript
0 Comments
Now openly admitted, governments and militaries around the world employ armies of keyboard warriors to spread propaganda and disrupt their online opposition. Their goal? To shape public discourse around global events in a way favorable to their standing military and geopolitical objectives. Their method? The Weaponization of Social Media.
U.S. President Donald Trump on Friday, January 19, 2018 said he signed into law a bill renewing the National Security Agency’s warrantless internet surveillance program. “Just signed 702 Bill to reauthorize foreign intelligence collection,” Trump wrote on Twitter, referring to legislation passed by the U.S. Congress that extends Section 702 of the Foreign Intelligence Surveillance Act (FISA). The law is renewed for six years and with minimal changes the National Security Agency (NSA) program, which gathers information from foreigners overseas and also collects an unknown amount of communications belonging to Americans. Without Trump’s signature, Section 702 had been set to expire on Friday, though intelligence officials had said the surveillance program could continue to operate until April. Under the law, the NSA is allowed to eavesdrop on vast amounts of digital communications from foreigners living outside the United States via U.S. companies like Facebook, Verizon, and Google. But the program also incidentally scoops up Americans’ communications, including when they communicate with a foreign target living overseas, and can search those messages without a warrant. The White House, U.S. intelligence agencies and congressional Republican leaders have said the program is indispensable to national security, vital to protecting U.S. allies and needs little or no revision. Privacy advocates say it allows the NSA and other intelligence agencies to grab data belonging to Americans in a way that represents an affront to the U.S. Constitution. ReferencesVolz, D. (2018). Trump signs bill renewing NSA's internet surveillance program. [online] Reuters. Available at: https://www.reuters.com/article/us-usa-trump-cyber-surveillance/trump-signs-bill-renewing-nsas-internet-surveillance-program-idUSKBN1F82MK?feedType=RSS&feedName=domesticNews [Accessed 23, Jan. 2018].
From Corbettreport.com: When WWII ended and the American deep state welded the national security establishment into place with the National Security Act, the world entered into a new era: the era of the military-industrial complex. But when the Cold War ended and the “Clash of Civilizations” became the new existential threat, the deep state found an opening for another paradigm shift. As the all-pervasive threat of terrorism became the carte blanche for total surveillance, the powers-that-shouldn’t-be found the organizing principal of our age would not be military hardware, but data itself. Welcome to the age of the information-industrial complex. This is The Corbett Report. Of all the things that President Dwight D. Eisenhower did during his years in office, it is for a single phrase from his farewell address that he is best remembered today: “the military-industrial complex.” “In the councils of government, we must guard against the acquisition of unwarranted influence, whether sought or unsought, by the military-industrial complex. The potential for the disastrous rise of misplaced power exists and will persist.” It is not difficult to see why these words passed so quickly into the political lexicon. Think of their explanatory power. Why did the US use inflated estimates of Russian missile capabilities to justify stockpiling a nuclear arsenal that was more than sufficient to destroy the planet several times over? The military-industrial complex. Why did America send 50,000 of its own to fight and die in the jungles of Vietnam, killing untold millions of Vietnamese (not to mention Cambodians)? The military-industrial complex. Why did the US use the public’s fear and anger over 9/11 and a phony panic over non-existent weapons of mass destruction to justify the illegal invasion and trillion dollar occupation of Iraq? The military-industrial complex. Why did Nobel Peace Prize laureate Obama expand the fictitious “war on terror” into Pakistan and Yemen and Somalia, refuse to close Guantanamo despite his earlier promises to the contrary, commit US forces to “kinetic military action” in Libya without so much as seeking Congressional approval, and launch a new era of covert drone warfare? The military-industrial complex. Why has Trump not only continued but further expanded the US military presence in Africa, increased US aid to Israel and Saudi Arabia, actively enabled the war crimes in Yemen that have led to the largest cholera outbreak in human history, and killed more civilians in his first 9 months in office than former drone-king Obama killed in his entire 8 year presidency? The military-industrial complex. When you think about it, it’s rather remarkable that such a phrase was ever uttered by a President of the United States, much less a former five-star general. Could you imagine any modern-day President talking about something like the “military-industrial complex” and its attempted “acquisition of unwarranted influence” without immediately dismissing the idea as a conspiracy theory? Over the decades there has been much speculation about Eisenhower’s use of the phrase, and what precisely he was warning against. Some have argued that the phrase was prompted by Eisenhower’s discovery that the Rand Corporation was grossly misrepresenting the Soviet’s military capabilities to John F. Kennedy, who ended up using the Rand invented (and completely fictitious) “missile gap” threat as a cornerstone of his 1960 presidential election campaign. Whatever the case, it is perhaps time to revisit Eisenhower’s most famous speech. What Eisenhower is ultimately describing is the rise of American fascism; the merger of government and corporate power. What term can better capture the nature of early 21st century American political life? Is there any longer any doubt that the military-industrial complex has reached its ultimate expression in firms like Blackwater (aka “Xe” aka “Academi”) and its military contractor brethren? Is there any other word but ‘fascism’ to describe a state of affairs when a Secretary of Defense can commission a study from a private contractor to examine whether the US military should be using more private contractors, only for that same Secretary of Defense to leave office and become president of the company that conducted the study, only to leave that company to become Vice President of the US and begin waging a war that relies heavily on no-bid contracts awarded to that same company based on the recommendation that it made in its original study? Yet this is precisely the case of Dick Cheney and Halliburton. It would be difficult to think of a more blatant example of the military-industrial complex fascism that Eisenhower was warning of. But as it turns out, there was another warning about fascism embedded in that farewell address that has received far less attention than the ‘military-industrial complex’ formulation, perhaps because there is no catchphrase hook to describe it: “Today, the solitary inventor, tinkering in his shop, has been overshadowed by task forces of scientists in laboratories and testing fields. In the same fashion, the free university, historically the fountainhead of free ideas and scientific discovery, has experienced a revolution in the conduct of research. Partly because of the huge costs involved, a government contract becomes virtually a substitute for intellectual curiosity. For every old blackboard there are now hundreds of new electronic computers.” Given that this warning came in 1961, before the age of communications satellites or personal computers or the internet, it was a remarkably prescient observation. If scientific research half a century ago was dominated by federal grants and expensive computer equipment, how much more true is that for us today, half a century later? So what is the problem with this? As Ike explained: “Yet, in holding scientific research and discovery in respect, as we should, we must also be alert to the equal and opposite danger that public policy could itself become the captive of a scientific-technological elite.” Here again the warning is of fascism. But instead of the military-industrial fascism that dominated so much of the 20th century, he was describing here a new fascistic paradigm that was but barely visible at the time that he gave his address: a scientific-technological one. Once again, the threat is that the industry that grows up around this government-sponsored activity will, just like the military-industrial complex, begin to take over and shape the actions of that same government. In this case, the warning is not one of bombs and bullets but bits and bytes, not tanks and fighter jets but hard drives and routers. Today we know this new fascism by its innocuous sounding title “Big Data,” but in keeping with the spirit of Eisenhower’s remarks, perhaps it would be more fitting to call it the “information-industrial complex.” The concept of an information-industrial complex holds equally explanatory power for our current day and age as the military-industrial complex hypothesis held in Eisenhower’s time. Why is a company like Google going to such lengths to capture, track and database all information on the planet? The information-industrial complex. Why were all major telecom providers and internet service providers mandated by federal law to hardwire in back door access to American intelligence agencies for the purpose of spying on all electronic communications? The information-industrial complex. Why would government after government around the world target encryption as a key threat to their national security, and why would banker after banker call for bitcoin and other cryptocurrencies to be banned even as they plan to set up their own, central bank-administered digital currencies? The information-industrial complex. The effects of this synthesis are more and more felt in our everyday lives. Every single day hundreds of millions of people around the world are interfacing with Microsoft software or Apple hardware or Amazon cloud services running on chips and processors supplied by Intel or other Silicon Valley stalwarts. Google has become so ubiquitous that its very name has become a verb meaning “to search for something on the internet.” The 21st century version of the American dream is encapsulated in the story of Mark Zuckerberg, a typical Harvard whizkid whose atypical rise to the status of multi-billionaire was enabled by a social networking tool by the name of “Facebook” that he developed. But how many people know the flip side of this coin, the one that demonstrates the pervasive government influence in shaping and directing these companies’ rise to success, and the companies’ efforts to aid the government in collecting data on its own citizens? How many know, for instance, that Google has a publicly acknowledged relationship with the NSA? Or that a federal judge has ruled that the public does not have the right to know the details of that relationship? Or that Google Earth was originally the brainchild of Keyhole Inc., a company that was set up by the CIA’s own venture capital firm, In-Q-Tel, using satellite data harvested from government “Keyhole” class reconnaissance satellites? Or that the former CEO of In-Q-Tel, Gilman Louie, sat on the board of the National Venture Capital Association with Jim Breyer, head of Accel Partners, who provided 12 million dollars of seed money for Facebook? Or that in 1999, a back door for NSA access was discovered in Microsoft’s Windows operating system source code? Or that Apple founder Steve Jobs was granted security clearance by the Department of Defense for still-undisclosed reasons while heading Pixar in 1988, as was the former head of AT&T and numerous others in the tech industry? The connections between the IT world and the government’s military and intelligence apparatus run deep. In fact, the development of the IT industry is intimately intertwined with the US Air Force, the Department of Defense and its various branches (including, famously, DARPA), and, of course, the CIA. A cursory glance at the history of the rise of companies like Mitre Corporation, Oracle, and other household electronics and software firms should suffice to expose the extent of these relations, and the existence of what we might dub an “information-industrial complex.” But what does this mean? What are the ramifications of such a relationship? Although the signs have been there for decades, perhaps the most startling example of what lies at the heart of this relationship has been revealed by the whistleblowers at the heart of the National Security Agency, one of the most secretive arms of the American intelligence apparatus. While Edward Snowden has received the most attention with his “revelation” of the PRISM program, much of the information about the NSA’s ability to surveil all electronic communications has been revealed over the past decade by NSA whistleblowers like Russ Tice, William Binney, Thomas Drake and J. Kirk Wiebe, third-party contractors like Snowden and AT&T whistleblower Mark Klein, and independent journalists like James Bamford. Together, the story they tell is of a truly Orwellian society in which all communications are being captured and analyzed by the NSA, and, with the advent of facilities like the new data center in Utah, presumably stored indefinitely for use at any future time in any future investigation for any pretense by anyone with authorization to access that data. According to Snowden, this includes lowly third-party contractors like himself operating at NSA subcontractors like Booz Allen Hamilton in the vast (and expanding) private intelligence industry that has grown up around the information-industrial complex in the exact same way as private military contractors like Blackwater formed around the military-industrial complex. In some ways, this information-industrial complex is even more insidious than its military-industrial counterpart. For all of the ills caused by the military-industrial complex (and there are many), at the very least it required some sort of excuse to drain the American people’s resources, and its failures (like the Vietnam quagmire or the debacle in Iraq) happened in the clear light of day. In the information-industrial complex, where vast spying programs happen in the shadows and under the cover of “national security” it takes whistleblowers and insiders willing to risk it all even to find out what is being done by these shadowy agencies and their private sector contractors. Even worse, the entire Orwellian spy grid is being run on the flimsiest of pretenses (the “war on terror”) that has no defined end point, and “justifies” turning that spy grid inward, on the American people themselves. Surely Eisenhower never envisaged the monstrosity that this information-industrial complex has become, but the foresight he saw in identifying its early stages over half a century ago is remarkable. The problem is that we are even further away from heeding the warning that he delivered in that 1961 address than we were at that time: “It is the task of statesmanship to mold, to balance, and to integrate these and other forces, new and old, within the principles of our democratic system – ever aiming toward the supreme goals of our free society.” If only this was the rhetoric that was shaping today’s debate on the issue, instead of the well-worn canard that we must “strike a balance” between freedom and security. Sadly, until such time that the National Security Act of 1947 is repealed and the cover of national security is lifted from the dark actors that populate this sector, the information-industrial complex is unlikely to be quashed-or even hampered-anytime soon. ReferencesCorbett, J. (2017). Episode 325 – The Information-Industrial Complex : The Corbett Report. [online] Corbettreport.com. Available at: https://www.corbettreport.com/episode-325-the-information-industrial-complex/ [Accessed 18 Dec. 2017].
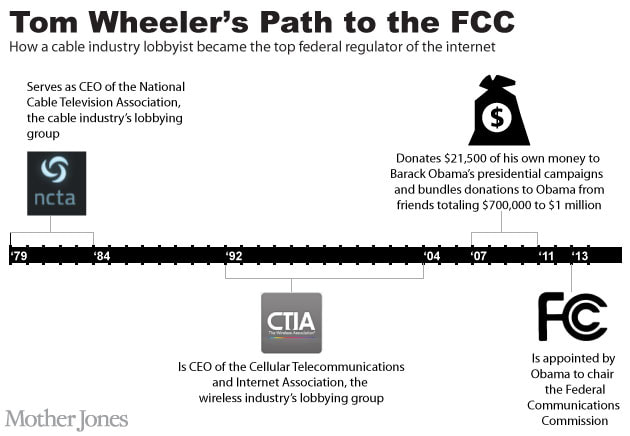
The Federal Communications Commission (FCC) chairman, Ajit Pai, announced plans to dismantle net neutrality November 21, 2017. Pai said it best, "Under my proposal, the federal government will stop micromanaging the Internet. Instead, the FCC would simply require Internet service providers to be transparent about their practices so that consumers can buy the service plan that’s best for them and entrepreneurs and other small businesses can have the technical information they need to innovate." Net Neutrality: the principle that Internet service providers must treat all data on the Internet the same, and not discriminate or charge differently by user, content, website, platform, application, type of attached equipment, or method of communication. Net neutrality refers to a network, the Internet, in which all data is regulated, or treated equally. Under the principle of net neutrality, Internet services providers (ISPs) are unable to intentionally block, slow down or charge money for specific websites and online content. This means, for instance, that your ISP can't form a special deal with a big company like Netflix or Amazon to let their data pass through the network more quickly or downgrade other sites to an Internet "slow lane" where data passes to users more slowly. At first glance, net neutrality is good for the average Internet user. But there is much more to net neutrality than that, and it starts with Tom Wheeler. Tom Wheeler: The Cable Industry Lobbyist and Top Federal Regulator of the Internet Tom Wheeler, former FCC Chairman, former President of the National Cable and Telecommunications & Internet Association, and former CEO of the Cellular Telecommunications and Internet Association. Wheeler is a lobbyist for the very industry he is supposedly regulating. Now, net neutrality wasn't Wheeler's idea, but was rather proposed under the Obama Administration. The official regulatory plan was published in a 400 page document. The FCC reclassified ISPs as common carriers under Title II of the Federal Communications Act of 1934, as well as Title III of the same Act and Section 706 of the Telecommunications Act of 1996. Now the FCC has the authority to regulate ISPs, even at the rates at which they charge their customers. In Plain English In other words, under net neutrality (more specifically Title II), the Internet is classified by the U.S. government as a public utility. This is a blank check for government control across the board. This means that local, state, and federal fees that apply specifically to the Title II services will create billions of dollars in new charges that will be pushed on to American Internet users. It means that any branch of FCC commissioners will be able to wield powers to enforce the rules over any service on the Internet in any way they see fit. Essentially, the future of the Internet lies in the hands of the FCC under net neutrality. The FCC called it a triumph of “free expression and democratic principles.” It was anything but. It was actually a power grab, creating an Internet communication cartel not unlike the way the banking system works under the Federal Reserve. Goodbye Net Neutrality; Hello Competition Net neutrality closed down market competition by putting government and its corporate backers in charge of deciding who can and cannot play in the market. It erected hurdles for smaller companies to jump over while hugely subsidizing the largest content providers. In effect, with net neutrality, no price reductions in internet service would be seen. Your bills may go up and there would be very little competition. In other words, it was like all government regulation: most of the costs were unseen, and the benefits were concentrated in the hands of the ruling class. Think of the medical industry, which is now entirely owned by a non-competitive cartel of industry insiders. This would be the future of the internet under net neutrality. Goodbye net neutrality! No more government-managed control of the industry. No more price fixing. No more of the largest players using government power to protect their monopoly structure. The end of net neutrality is the best single deregulatory initiative yet taken by the Trump administration. We should take our deregulation where we can get it. ReferencesCorbett, J. (2015). Net “Neutrality,” or, How To Regulate the Internet to Thunderous Applause : The Corbett Report. [online] Corbettreport.com. Available at: https://www.corbettreport.com/net-neutrality-or-how-to-regulate-the-internet-to-thunderous-applause/ [Accessed 7 Dec. 2017].
Tucker, J. (2017). Goodbye Net Neutrality; Hello Competition. [online] Fee.org. Available at: https://fee.org/articles/goodbye-net-neutrality-hello-competition/ [Accessed 7 Dec. 2017]. The launch of the so-called AWS Secret Region comes six years after AWS introduced GovCloud, its first data-center region for public-sector customers. AWS has since announced plans to expand GovCloud. The new Secret Region signals interest in using AWS from specific parts of the U.S. government. In 2013, AWS and the CIA signed a $600 million contract to keep up with big data analytics. That event singlehandedly helped Amazon in its effort to sign up large companies to use its cloud, whose core services have been available since 2006. Today AWS counts companies such as Comcast, Hess, Intuit and Lionsgate as customers. AWS' competitors include Microsoft, Google, IBM and Oracle. "With the launch of this new Secret Region, AWS becomes the first and only commercial cloud provider to offer regions to serve government workloads across the full range of data classifications, including Unclassified, Sensitive, Secret, and Top Secret," Amazon said in a blog post. The new region is available to customers as a result of AWS' contract with the intelligence community's Commercial Cloud Services, or C2S, group, and it will meet certain government standards, Amazon said. But the region will also be accessible for U.S. government organizations that aren't part of the intelligence community so long as they have their own "contract vehicles" and sufficient secret-level network access, Amazon said. ReferencesAmazon Web Services. (2017). Announcing the New AWS Secret Region | Amazon Web Services. [online] Available at: https://aws.amazon.com/blogs/publicsector/announcing-the-new-aws-secret-region/ [Accessed 22 Nov. 2017].
Konkel, F. (2017). Sources: Amazon and CIA ink cloud deal -- FCW. [online] FCW. Available at: https://fcw.com/articles/2013/03/18/amazon-cia-cloud.aspx [Accessed 22 Nov. 2017]. Novet, J. (2017). Amazon launches a cloud service for US intelligence agencies. [online] CNBC. Available at: https://www.cnbc.com/2017/11/20/amazon-launches-aws-secret-region.html?__source=twitter%7Cmain [Accessed 22 Nov. 2017]. Many YouTube videos covering certain topics or having particular opinions, shared by alternative media sources, have been flagged, censored, demonetized, or flat-out removed. YouTube (owned and operated by Alphabet Inc.) claimed this was due to tighter enforcement of existing rules, even if true this will restrict the type of content that gets made and is a form of censorship. We are seeing a concerted effort to such down free speech on the Internet, under the name of "fake news", "Russian propaganda", etc. A solution to combat this internet censorship lies in an alternative decentralized platform: BitChute. What is BitChute? BitChute is a peer-to-peer (p2p) video sharing platform powered by WebTorrent, with a mission to put people and free speech first. Rather than needing massive data centers with humongous bandwidth costs, torrents are open-source and depend on many people sharing videos from their home computers. In other words, it is decentralized and depends on people to use it; in fact, the more people that use the platform, the faster videos will load. While this has been possible for many years through bit torrent, bit torrent applications have steep learning curves; this site aims to make the torrent experience seamless by working entirely in the web browser. Unlike Youtube, BitChute is a p2p network, thus the user can host content as well as watch. Right now, BitChute will work in Firefox and Chrome Internet browsers. BitChute is not alone in the wake of the battle for free speech; there are various other video sharing platforms dedicated to prevent Internet censorship, including but not limited to: ReferencesBitChute. (2017). BitChute is a peer to peer video sharing platform. [online] Available at: https://www.bitchute.com/faq [Accessed 3 Oct. 2017].
The global war on terror has entered the digital age and it’s no longer a question of if there will be an attack on the world wide web but when! In this video Dan Dicks of Press For Truth speaks with James Corbett of The Corbett Report about what a possible cyber attack scenario might look like, who the perpetrators are likely to be, who the scapegoat will be to take the fall and most importantly what we all can do about it BEFORE it happens.
In the wake of London and Manchester, politicians around the world are trying to convince the public that the free flow of information on the internet is a terror threat. In reality, independent online media are exposing the real terrorists: the politicians and their deep state handlers who are funding, arming, aiding and enabling false flag terror.
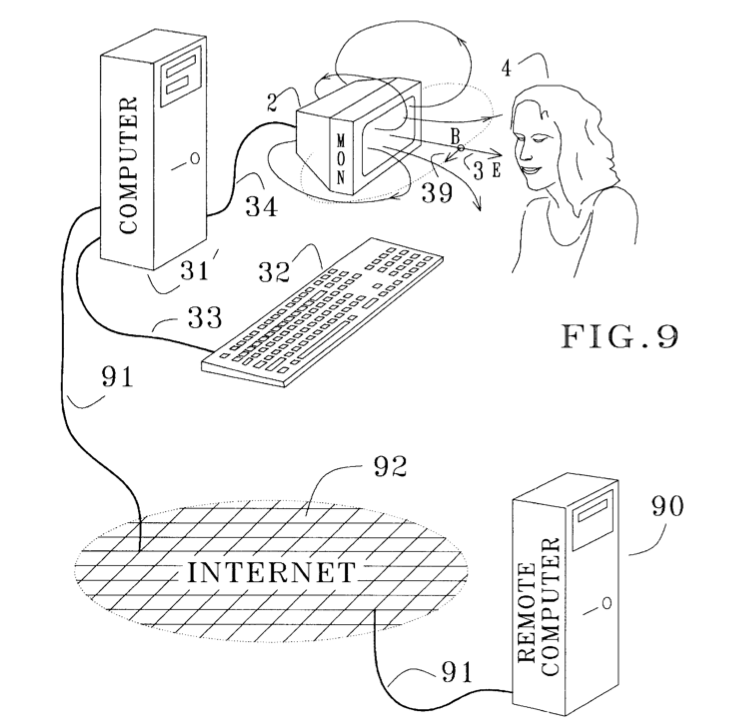
"Many computer monitors and TV tubes, when displaying pulsed images, emit pulsed electromagnetic fields of sufficient amplitudes to cause such excitation. It is therefore possible to manipulate the nervous system of a subject by pulsing images displayed on a nearby computer monitor or TV set." The pulsing image displayed on a computer monitor or television is able to be embedded in the material of a simple video or computer program, or it may be overlaid by modifying a videostream, as either a radio frequency or video signal. These pulsating EMFs are capable of exciting the senses in nearby subjects even if the images displayed are pulsed at subliminal intensity; the EMFs are able to affect the nervous system without the individual even being aware of it.
The implementations of this patent adapt to the source of video that drives the monitor, whether it be a computer program, a TV broadcast, a video tape or a DVD. In fact, this technology is basic enough to run on Windows 95 or 98. Patent Warning "Certain monitors can emit EMF pulses that excite a sensory resonance in a nearby subject, through image pulses that are so weak as to be subliminal. This is unfortunate since it opens a way for mischievous application of the invention, whereby people are exposed unknowingly to manipulation of their nervous systems for someone else’s purposes. Such application would be unethical and is of course not advocated. It is mentioned here in order to alert the public to the possibility of covert abuse that may occur while being online, or while watching TV, a video, or a DVD." Just because the technology exists, doesn't mean that it being used on every individual. However, it is paramount to be aware of this technology; it already exists, and is quite frankly old technology - imagine what technology exists today. Let us not be naive of the powers that shouldn't be who have control over this technology. While there is not much we can do to combat this technology in our modern society, there is no excuse to be ignorant. Although, it is also important to become aware of potential neurotic behaviors, as this can also be detrimental to your health and wellness. References
“Monsanto even started the aptly-named ‘Let Nothing Go’ program to leave nothing, not even Facebook comments, unanswered; through a series of third parties, it employs individuals who appear to have no connection to the industry, who in turn post positive comments on news articles and Facebook posts, defending Monsanto, its chemicals, and GMOs,” More concerning, revealed by the documents, Monsanto allegedly “quietly funnels money to ‘think tanks’ such as the ‘Genetic Literacy Project’ and the ‘American Council on Science and Health”– organizations intended to shame scientists and highlight information helpful to Monsanto and other chemical producers,”. At the US District Courthouse in San Francisco, the plaintiffs claim that exposure to the herbicide Roundup caused them or their relatives to develop non-Hodgkin lymphoma, while Monsanto concealed the potential risks. Glyphosate, the active ingredient in Roundup, has been classified as a probable carcinogen, according to the International Agency for Research on Cancer, a specialized cancer agency of the World Health Organization. The claims against Monsanto are backed up by a group of emails, used as evidence in the court, composed by Monsanto executives, instructing third parties to "ghost-write" sections of "scientific" papers, upon which some "scientists" would just edit and sign their names on the publication. “A less expensive/more palatable approach might be to involve experts only for the areas of contention, epidemiology and possibly MOA (depending on what comes out of the IARC meeting), and we ghost-write the Exposure Tox & Genetox sections,” the letter’s excerpt reads. “An option would be to add Greim and Kier or Kirkland to have their names on the publication, but we would be keeping the cost down by us doing the writing and they would just edit & sign their names so to speak. Recall that is how we handled Williams Kroes & Munro, 2000.” Monsanto denies the allegations, continuing to claim that "glyphosate does not cause cancer". References Monsanto Accused of Hiring Army of Trolls to Silence Online Dissent – Court Papers | Global Research - Centre for Research on Globalization. (2017). Globalresearch.ca. Retrieved 16 May 2017, from http://www.globalresearch.ca/monsanto-accused-of-hiring-army-of-trolls-to-silence-online-dissent-court-papers/5588396 Ruskin, G. (2017). MDL Monsanto Glyphosate Cancer Case Key Documents & Analysis. U.S. Right to Know. Retrieved 16 May 2017, from https://usrtk.org/pesticides/mdl-monsanto-glyphosate-cancer-case-key-documents-analysis/
|
This feed contains research, news, information, observations, and ideas at the level of the world.
Archives
May 2024
Categories
All
|
||||||||||||||||||||||||




 RSS Feed
RSS Feed

